#intel
Episodes
 213 - The lost art of System Architecture
213 - The lost art of System Architecture
In the rapidly evolving fields of software engineering and architecture, it is crucial to combine vision, creativity, and experienced judgment to ensure long-lasting advancement. In our recent episode of 'Embracing Digital Transformation,' Darren interviews George Davelman, CTO of Vixtera, who provided invaluable insights, encouraging us to approach the challenges of technological evolution with a practical mindset.
 143 - Use Cases in Confidential Computing
143 - Use Cases in Confidential Computing
In this episode of Embracing Digital Transformation Dr. Anna Scott continues her conversation with Ibett Acarapi and Jesse Schrater about Confidential Computing and their uses in AI, and software development.
 110 - Securing the Supply Chain
110 - Securing the Supply Chain
In this episode, Darren talks with Lieutenant General Thomas Horlander, who recently joined the Intel Public Sector Team, about the microelectronics supply chain and national security.
 80 - Meeting Intel's Cloud Solution Architects
80 - Meeting Intel's Cloud Solution Architects
Darren Pulsipher, Chief Solution Architect, Intel, talks with Intel’s top cloud solution architects Stephen Holt, Kiran Agrahara, Sarah Musick, and Todd Christ about how they can help organizations, at no charge, migrate to the cloud and optimize their workloads.
 76 - Day in the Life of a Cloud Solution Architect
76 - Day in the Life of a Cloud Solution Architect
On this episode, Darren talks with Kiran Agrahara about what Intel Cloud Solution Architects (CSAs) do in a day to benefit not only cloud service providers (CSPs), but end users.
 30 - Application Portability with OneAPI
30 - Application Portability with OneAPI
With oneAPI, Intel has created a unified software environment for development, geared toward data processing. Gretchen Stewart, Chief Data Scientist, Public Sector, Intel, discusses this technology with Darren Pulsipher, Chief Solution Architect, Intel, that eliminates the need for using a different language for different architectures.
 17 - Elastic Search & Intel Optane DCPMM
17 - Elastic Search & Intel Optane DCPMM
Darren Pulsipher shows how he increased Elasticsearch performance using Intel%92s Optane Persistent Memory in 100 percent app direct mode. His tests show an incredible performance increase of 2x. By doubling the throughput capacity, you can greatly decrease the number of servers in your Elasticsearch cluster.
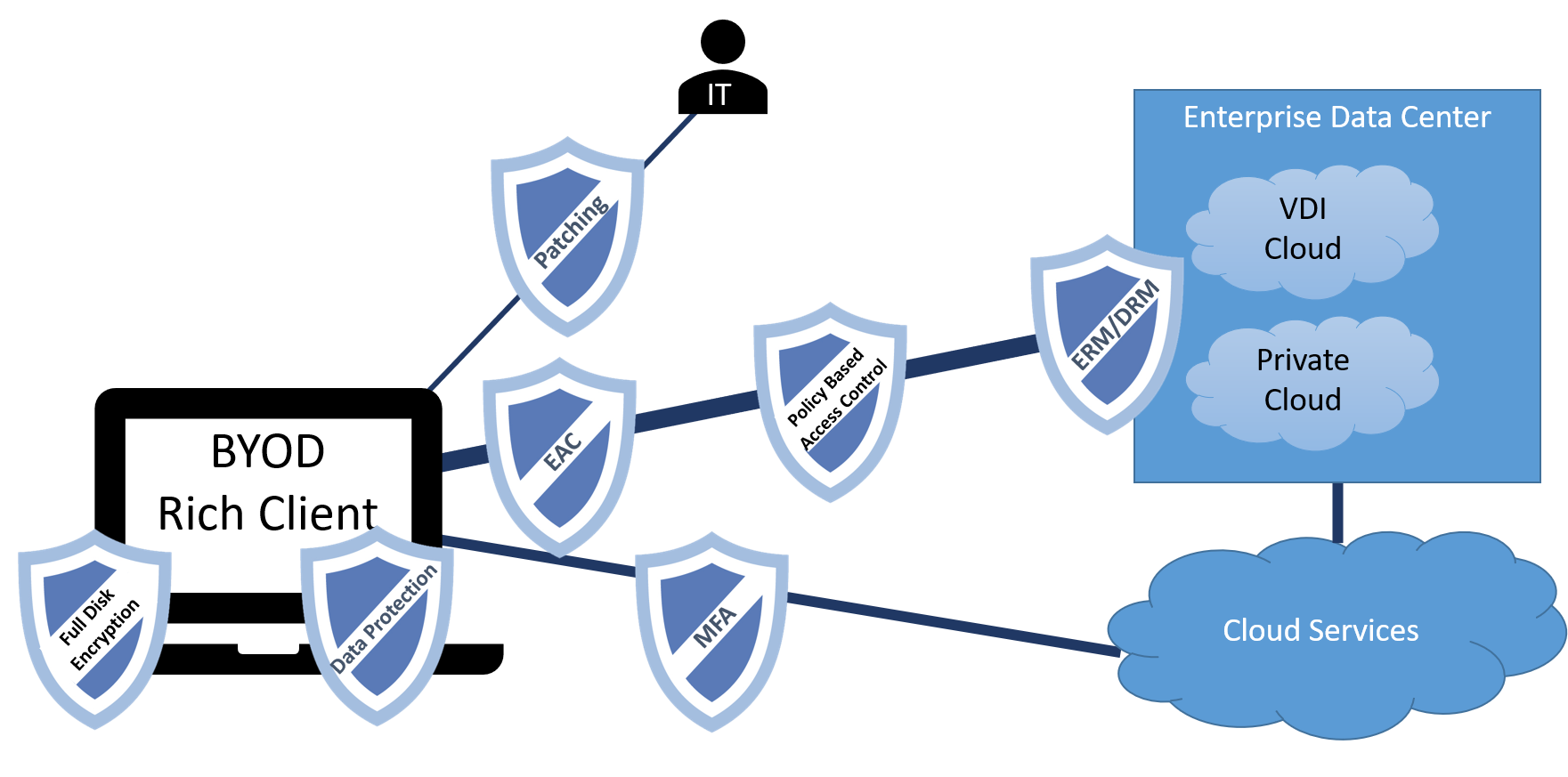 8 - Securing the Teleworker Part 2
8 - Securing the Teleworker Part 2
With many employees now working from home, how do you make sure they are working securely yet still give them the flexibility they need to get their jobs done? In this episode, Darren and special Guest Steve Orrin, CTO of Intel Federal, discuss how to leverage Intel technology to effectively help secure the teleworker.